A number of publicized web security breaches have thrust the importance of web hosting security into the public consciousness. It would be a mistake to believe that only large enterprises need to be concerned with the security of their web hosting.
Most people who use a hosting provider will purchase a plan that ranges between shared hosting and dedicated hosting. We trust that the hosting provider will be responsible for a number of security measures. Still, you should be familiar with the web hosting features they offer as this will allow you to guarantee the security of your web host and differentiate between real security risks and exaggerated security risks that are used as a way to sell unnecessary products.
Malware Scanners
Malware scanning is the process of scanning your website for malware. Many web host providers offer tools to do this, ranging from free to hundreds of dollars annually.
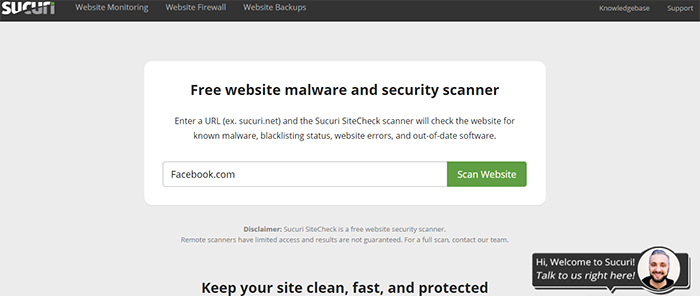
Sucuri SiteCheck is a free online web host malware scanning service. Using the service is pretty straightforward. When you visit the site, you’ll be presented with a text box. Put the address of your site in the box and hit scan website.
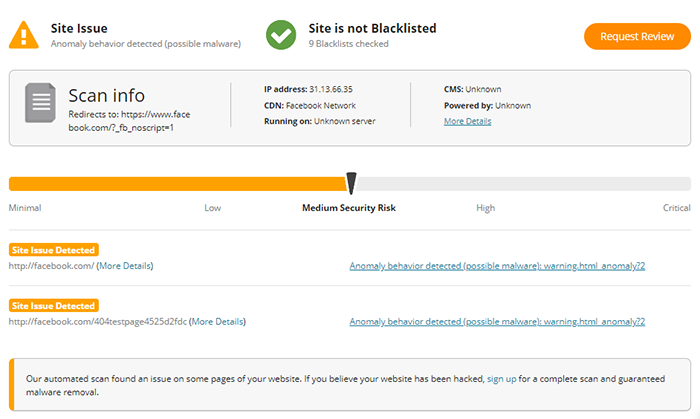
Once the scan is complete, you will be presented with a report that outlines any issues with malware that has been detected on your site. Sucuri offers paid plans in addition to the free services that they offer. These paid plans can be customized to scan your web host at regular intervals for malware.
Use Quality Web Hosting
Web hosting review sites may or may not present an unbiased view of a web hosting platform or company. Don’t get sucked in by flowery reviews that are in essence advertisements for a particular web hosting company. Instead, look at the hosting company’s features from a safety conscious standpoint. Although it should go without saying, avoid free hosts. They’re free for a reason.
While not an exhaustive list, these are some of the web host security features that identify quality web hosting:
- Backup and restore points
- Network monitoring
- SSL, firewalls, and DDOS prevention
- High accountability and disaster recovery
- Password and user access
- Code reviews
- Encryption
Protect Yourself against Brute Force Attacks
Brute force attacks are designed to gain access to your user account by repeatedly trying to guess the password of a user or a group of users. Without the proper protections in place, automated tools can subject your site to thousands of password attempts in seconds, allowing attackers to get around password-based authentication systems. A few steps that you can take include:
- Monitor server logs
- Use Captcha
- Instead of using a default port, edit the port line in your SSHD_config file
- Limit failed login attempts
- Limit logins to a set IP address or range
- Create a unique login URL

Avoid Excessive Plug-Ins
All plug-ins are susceptible to security breaches. There are two reasons why hackers target plug-ins. The first reason is that they have a massive user base. The second reason is the sheer amount of plug-ins that are available. The more plug-ins there are, the more possibilities exist for plug-ins to be exploited. Plug-Ins are used as attack vectors and can result in huge data loss.
It is recommended that you use as few plug-ins as possible. Here are some steps you may want to take in limiting plug-in use:
Choose Reputable Plug-Ins: Sites like WordPress provide information about plug-ins that you should pay attention to.
For example:
- Pay attention to the last update. How long ago was the plug-in updated? The more recent the update, the better.
- Check the number of active installs. While you may find reputable plug-ins that have a small number of installs, it’s best to stay away from plug-ins that have less than 1,000 active installs. Even if the plug-in is reputable, since it did not become popular, it may not be well-maintained and could be open for security breaches.
- The plug-ins average rating should be high. You do not want to use a plug-in that has a one star or a two-star rating.
- Delete plug-ins that you are no longer using. The best way for you to nullify a security risk is to get rid of it.
- Keep plug-ins updated. When the vulnerability of a plug-in is made public, plug-ins are updated to address these issues. Wordfence is a tool that many use to auto update the plug-ins.
- Delete or remove abandon plug-ins. If you are using a plug-in that has not been updated for a number of years, it is likely that the programmer behind it has abandoned the project. While an abandoned plug-in is not automatically a security risk, it is better to be safe than sorry.
Scan for Vulnerabilities
Most web applications have vulnerabilities. These vulnerabilities may include:
- Information leakage
- Issues with authentication and authorization
- XSS issues
ScanMyServer provides a comprehensive list of reports on a variety of potential vulnerabilities by performing security tests that include:
- Cross-site scripting
- PHP code injection
- HTTP header injection
- Blind SQL injection and more
Once the scan has been done, a scan report is compiled. An email is sent to you with a site vulnerability summary.
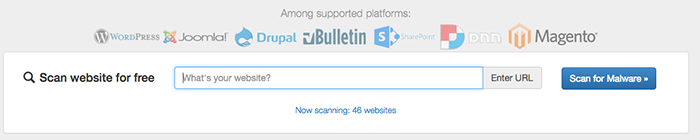
Quttera is another free website check. This free tool will scan your website and look for suspicious files, potentially suspicious files, malware, and other security issues.
SiteGuarding will allow you to scan your domain for inject spam, defacement, malware, website blacklisting, and more. The scanner works well with:
- Joomla
- WordPress
- Magento
It would be foolish for anyone to believe that security standards are not key to the well-being of a website. Education is the first step to protect your online reputation. Although your hosting provider will be responsible for the majority of security measures, the more you know, the better you will be able to verify that the security procedures are taking place.
Understanding and dealing with web hosting security can seem like a daunting task. However, webmasters who understand it and who work well with their hosting partner have a better chance of running their website without major disruptions in service. The list of online security threats is constantly growing. Your knowledge base needs to grow to allow you to combat these threats.
We hope you enjoyed this guide. Please leave any tips, comments, or questions in the comments section below.[/vc_column_text][/vc_column][/vc_row]


