In January 2025, Wordfence disclosed vulnerabilities in the ThemeREX Addons plugin for WordPress, affecting versions up to 2.33.0:
- The Local File Inclusion (LFI) issue, allowed authenticated users with contributor-level permissions or higher to include and execute arbitrary files on the server. This could theoretically result in security risks, such as bypassing access controls, exposing sensitive data (e.g., database credentials), or executing malicious PHP code on the server.
The issue was explicitly tied to misusing the trx_sc_reviews shortcode’s type attribute, which enabled attackers to exploit the vulnerability.
2. Unauthenticated Arbitrary File Upload Issue was found in trx_addons_uploads_save_data shortcode due to inadequate file type validation. This flaw allowed unauthenticated attackers to upload arbitrary files to the server, potentially leading to remote code execution.
While these vulnerabilities posed significant risks, ThemeREX developers acted swiftly and released a patched version (2.34.0) addressing both issues effectively.
What Should You Do?
To ensure your website remains secure, updating the ThemeREX Addons plugin to version 2.34.0 or later is crucial.
Follow these steps:
- Please make sure that ThemeREX Updater plugin is installed and activated in the Plugins section.
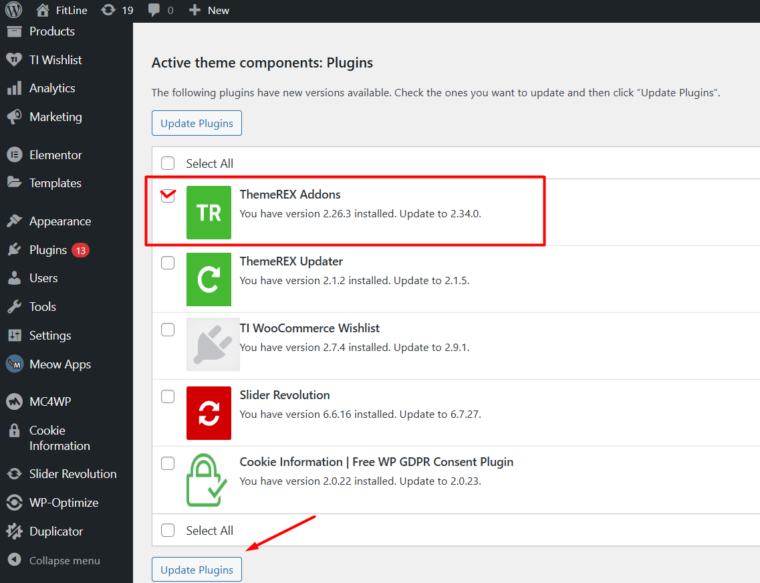
- Navigate to Dashboard -> Updates and check for available updates under ” Active Theme Components: Plugins.”
- Update the Themerex Addons plugin to version 2.34.0 or higher directly through TRX Updater for seamless results without manual intervention.
Solution for Earlier Themes
In case you are using one of our earlier themes, your Themerex Addons plugin has a much lower version than 2.33.x and cannot be updated automatically with Themerex Updater, you need to wait for a new theme update. As soon as it is released, you will find it in your Themeforest account -> Downloads.
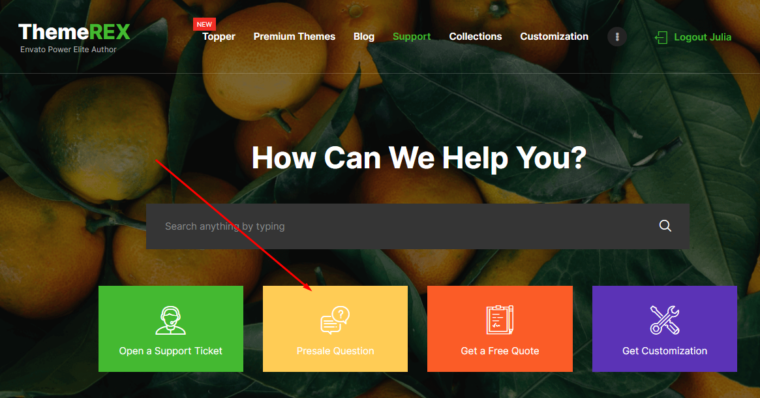
To get a quick fix, or if you need further assistance, please don’t hesitate to contact our Support Team via our Help Desk.
Additional Security Measures
While updating the plugin addresses the vulnerability, we recommend taking additional precautions:
- Perform a full malware scan on your website using server-side tools or professional incident response services.
- Review your website’s user accounts for any unauthorized changes.
- Regularly backup your website and monitor for suspicious activity.
We deeply apologize for any inconvenience caused by this issue and appreciate your understanding as we prioritize securing your websites.
On February 18, 2020 Wordfence has announced the disclosure of the vulnerability present in some versions of ThemeREX Addons plugin, a required plugin packaged with our themes.
Therefore, we wanted to notify our customers about the problem and elaborate on the quick fix.
First and foremost, our themes have different versions of the plugin so only some items were affected. Of course, ThemeREX developers have instantly found the problem and eliminated it. As a result, till February 20, we have successfully updated all the themes in question. In order to check if your theme has the problem, just have a look at the Change log at the bottom of the item description page onThemeforest.net If you can see “ThemeREX Addons vulnerability fixed” there, then you need to update the theme and the plugin to avoid the exploitation of this vulnerability.
In order to download the fixed theme version, please navigate to Downloads section of your Themeforest account. The steps to update Themerex Addons plugin in your WordPress admin are:
- Download the theme and find the included Themerex Addons plugin using the following path – theme_name/plugins/trx_addons/trx_addons.zip
- Then navigate to the Dashboard -> Plugins to deactivate and remove the current version of Themerex Addons plugin.
- Upload trx_addons.zip and activate it.
How to Apply the Fix Yourself
In addition, if you are not willing to update the theme, you may quickly make changes in files yourself. Just follow these steps:
- Log in to your Cpanel File Manager or use FTP client to access files on the server.
- Remove file wp-content/plugins/trx_addons/includes/plugin.rest-api.php If the file is not in your plugin, then there is no problem at all.
- Then, delete the following line of code in wp-content/plugins/trx_addons/trx_addions.php file:
require_once TRX_ADDONS_PLUGIN_DIR_INCLUDES . ‘plugin.rest-api.php’;
Congrats! You are done now. The vulnerability is successfully defused.
Moreover, our Tech Support Team is ready to help you solve the problem in our Help Desk. All you need is to submit a support ticket. If your support has expired, there is no need to purchase additional support. We will help you free of charge – just provide your website details using Presales Questions option.
Once again, take our deepest apologies for any inconvenience caused by this issue. We highly value our customers’ business, effort and time.



1 Comment
Ruben Alamina
I appreciate the post even if it’s late, since your team replied to the vulnerability post on WordFence, which you didn’t even include the post.
What was at risk, what was compromised, how can we make sure the site is secure after updating the plugin? I ask because I found an admin account that got created as soon as the vulnerability was found so I spent all night replacing files, looking for changes site wide, making a new database, migrating everything over to it, etc.
This kind of information needs to be really thourough in the future, is not enough to say you had a vulnerability and you fixed it via an update. The site could remain compromised even after updating if no other measure are taken by us and without information on how to proceed about this, it’s a mess and could be potentially big if the site control is taken over from you, for example.
Thanks for disclosing and I would ask you if possible, to allow customers with a valid (even if not current) purchase code to get in touch with your support for information in an event like this. Using a presales question option is not the right way to do it in my opinion.